Every year, as Hacker Summer Camp rolls around, there’s a surge in discussions about burner phones. And every year, I shake my head at some of the misconceptions floating around.
A true burner phone is a means of communication that isn’t easily tied to you. The goal is to remain anonymous—or at least harder to identify. But in today’s world of modern smartphones and interconnected services, staying off the radar takes more effort than just buying a cheap phone.
These are concepts from research, stories, fictional situations and in no way should be taken as advice or even accurate. I am not a lawyer and not everything mentioned here is legal everywhere, as far as I know. This article is meant to make you think about all the ways you can be associated with a new device **
Acquiring a Burner Phone the Right Way
If you order a phone online with your credit card and have it shipped to your home, it’s not a burner. Every phone has unique identifiers, and both the seller and service provider track them.
Here’s how to do it properly:
✅ Buy the phone in person.
✅ Use cash.
✅ Purchase it in your destination city, if possible. At the very least, don’t buy it where you live.
✅ Use a different carrier than your usual provider.
✅ Make sure the carrier accepts cash and offers prepaid options without registration.
The key is ensuring that neither the phone number nor the IMEI can be easily traced back to you.
Setting Up Your Burner Phone
Now that you have an unregistered phone with an ‘anonymous1‘ connection, what’s next?
🚫 Do NOT install your usual apps.
If your plan is to use Facebook, Twitter, or Bluesky, you don’t need a burner—just lock down your existing phone. If you just want a disposable device, that’s fine, but that’s not really a burner.
Keep in mind that social media apps track you and even analyze conversations to target ads. It’s best to avoid installing any apps you don’t absolutely need. If you have to use them, stick to the web version whenever possible.
🚫 Do NOT log into your normal accounts.
The moment you sign into your regular apps, that phone is tied to you. Game over.
If you absolutely need to use social media, create a brand-new account after you arrive at your destination. Don’t follow or connect with anyone—use it only for public drops, like scrubbed/anonymized photos, event updates, or encoded messages.
When the event is over, abandon the account. Never log into it again, especially outside the venue. Even accessing it at the airport can reveal which airline you flew and narrow down your travel details.
🚫 Do NOT text all your friends from the new number.
Even if your name isn’t tied to the account, your contacts, conversations, and habits can still give you away. A true burner setup means using a burner phone only with burner accounts—ideally, with others following the same protocol.
Plan ahead. Arrange a meetup at the event based on your risk model. If it’s just your usual group of friends grabbing beers, it’s simple.
When you meet, exchange your new Signal (or similar) handles. Don’t include the event name in the handle—keep it random, ideally a short two- or three-word phrase. Many password generators have a word-based option—use that for your username too.
Store all authentication directly on the phone, using the built-in password manager. Avoid biometrics. Instead, use a long PIN or complex pattern to lock the device.
When using the phone, do so in common areas, not your hotel room. This is actually a good time to use the conference WiFi.
Once you’ve established encrypted communication with your new accounts, then (and only then) share any additional contact info—like social media accounts for public updates or drop locations.
For retrieving photos, obfuscated messages, or taunts, do it once and never return. Let others poke around if they want, but don’t go straight to the source yourself.
🚫 Do NOT broadcast your burner phone info.
Announcing, “This is my burner phone, contact me here!” completely defeats the purpose. Instead, wait until you see people in person to share the number. We’ve already covered that.
Use only the burner phone for the SMS verification needed to create burner accounts—everything else should be built off that number. And before you leave town, destroy the phone.
The accounts should remain accessible for a while after you destroy the phone since verification was tied to that device. That gives you enough time to grab any necessary data, as we discussed.
✅ Create new accounts from the burner phone.
Use completely different usernames and handles. If you reuse known accounts, staying anonymous is impossible.
Create new accounts for the event from the burner phone. Use the burner phone number as the foundation for everything. Do not link these accounts to any existing emails or phone numbers—keep them completely separate.
✅ Reach out to new contacts from the burner phone.
Once the phone is set up, only contact the new accounts your contacts created for this event. Any associations made from this phone and number should be strictly limited to event-specific accounts.
If you only interact with your usual contacts, it becomes easier to trace the phone back to you. To help obscure your real activity, mix in unrelated interactions—browse random social media feeds, engage with different content, and add noise to bury the signal.
✅ Destroy the phone after the event.
Never log into those accounts again and never aNever log into those accounts again, and never access them from home or any familiar network. If you absolutely must check them later, use TOR or another method to cover your tracks. Ideally, you should only log into these accounts during the event.
All accounts should remain tied only to the burner phone number and the initial email used for setup. Do not use that email for anything else. Treat the social media accounts as dropboxes or for intentional public messages—nothing more.
At the end of the event, destroy the phone. Turning it on later, away from the event, risks exposing its unique identifier when it connects to a cell tower. That could link the account to a new location—potentially revealing where you live or even which terminal you flew out of.
✅ Use end-to-end encryption (E2EE) for communication.
For all your communications with contacts, use a good end-to-end encryptFor all communications with contacts, only use end-to-end encrypted (E2EE) messaging. As discussed, E2EE ensures that only the intended recipient can decrypt your messages using their private key.
Signal is a solid choice, and Session looks promising as well. With the latest updates in iPhone 18, you can enable E2EE in the Messenger app—but remember, you should only use new accounts. Keep Apple Messenger locked down for personal use at home. For everything else, use Signal whenever possible.
Never use the same accounts on your burner phone as you do on your regular phone.
Additional Security Considerations
If your safety is at risk—whether due to a domestic situation or an oppressive government—your approach needs to be even more meticulous.
🔹 Think about the tools you’re using. If you’re on an iPhone, create a new Apple ID, enable Lockdown Mode, disable location services, and remove unnecessary apps. On Android, do the same: new Google account, minimal apps, and as many tracking features disabled as possible.
🔹 SMS is not secure. Assume all texts are monitored. If you must use SMS, keep messages vague and avoid names or recognizable phrases.
🔹 Avoid logging into personal sites or services. If you only contact the same people on the same platforms, it’s not hard to link your burner phone to your real identity.
🔹 Be cautious with links. Many contain trackers, which can instantly associate your burner with your main accounts.
Final Thoughts

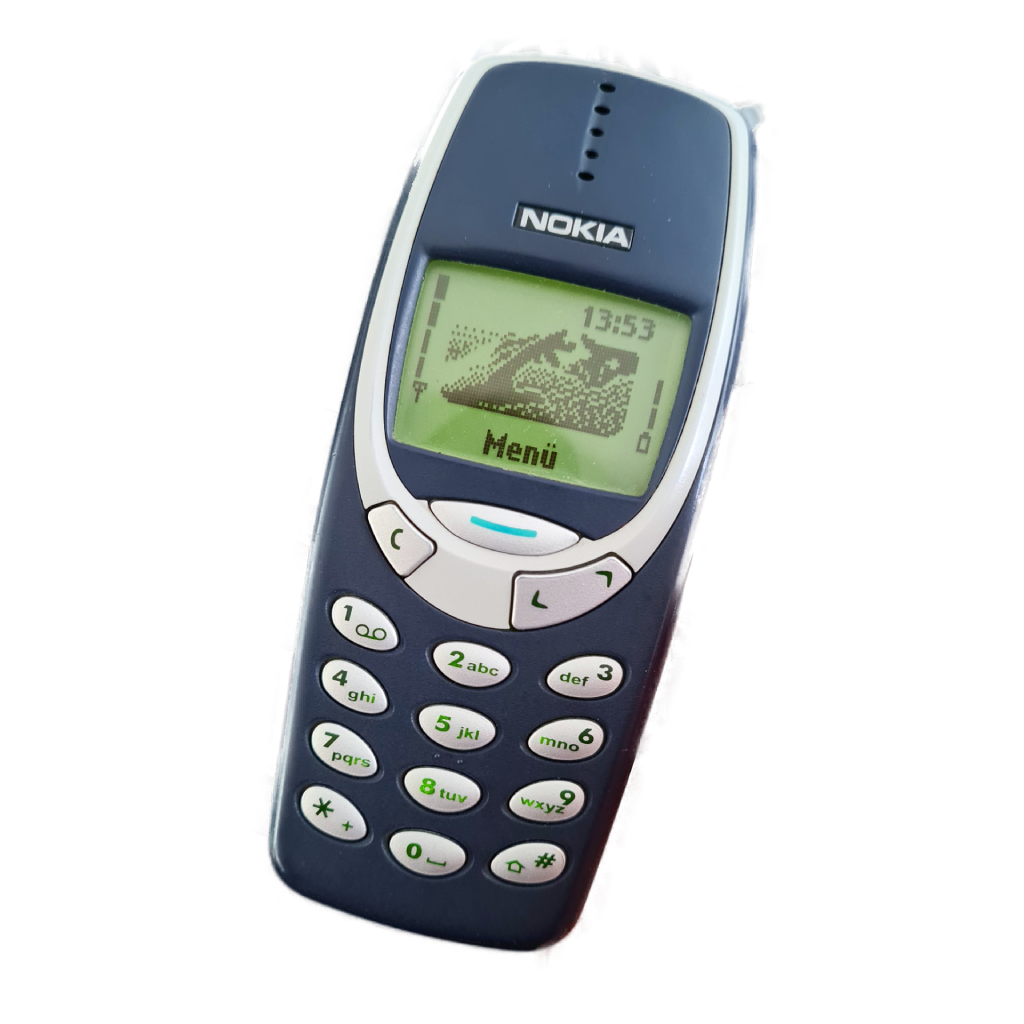
Your approach depends on your threat model and risk tolerance. Old-school burner phones were simple—no smart features, fewer risks. Modern burners require much more effort to keep your identity separate.
If you just need a phone you can discard after an event to avoid malware or tracking, you’re better off securing your existing phone:
🔸 Keep your device updated.
🔸 Watch for security warnings, like untrusted certificates.
🔸 Avoid clicking “OK” on anything suspicious, especially on public WiFi.
A burner phone isn’t a magic cloak of invisibility. It’s a tool—and like any tool, how well it works depends on how well you use it.
- Not really ↩︎